Control certificate lifecycle management in the cloud is essential for ensuring security and compliance. It encompasses key stages such as creation, issuance, management, renewal, and revocation of certificates. Best practices include defining certificate attributes, automating workflows, and conducting regular audits. Effective revocation processes address compromised certificates to mitigate risks. Automation plays a significant role by facilitating real-time monitoring and compliance checks. For a deeper understanding of enhancing security and compliance strategies, further details will be explored.
Key Takeaways
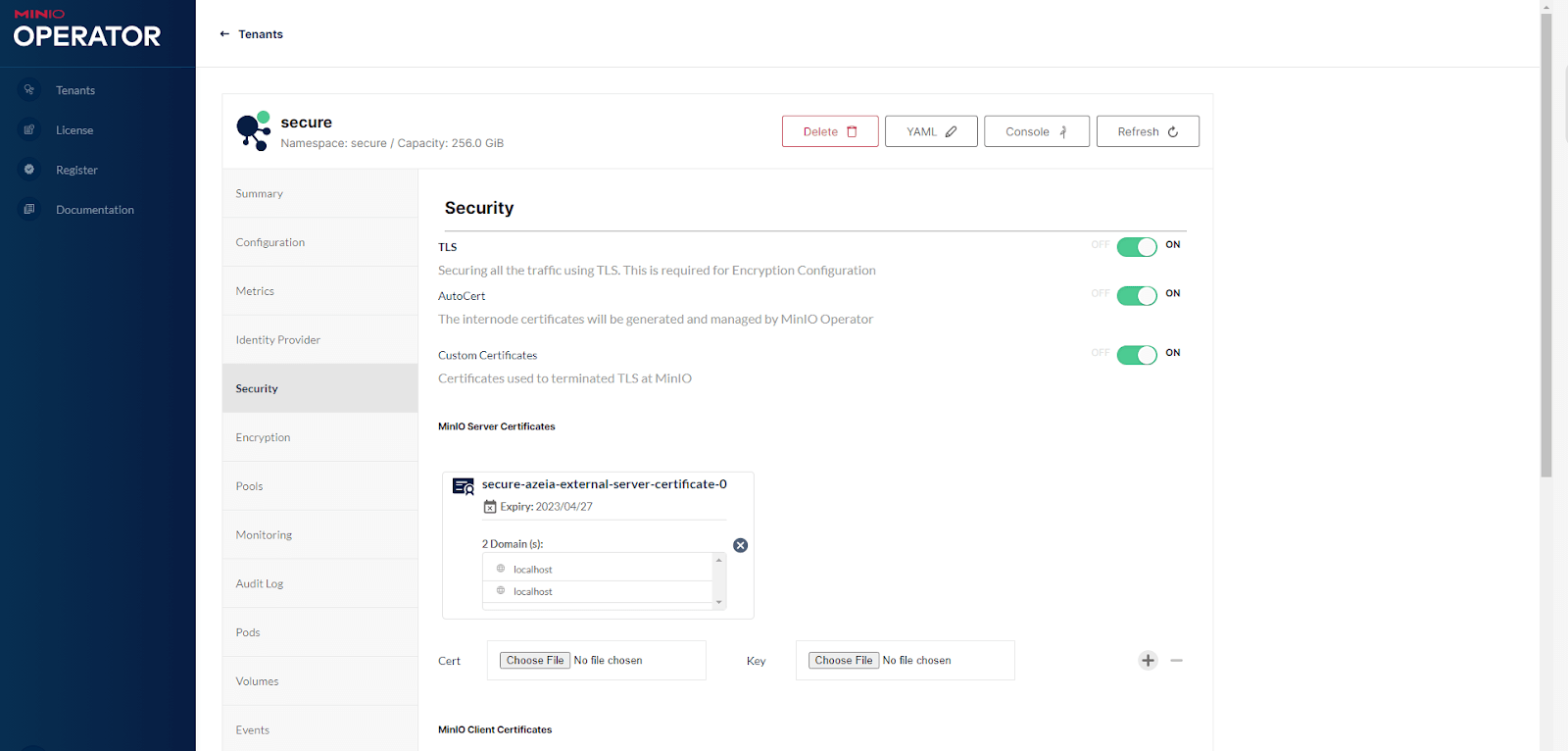
- Control certificates enhance cloud security by authenticating user and device identities, preventing unauthorized access and data breaches. The certificate lifecycle includes creation, issuance, management, and decommissioning, with a focus on compliance and security policies. Regular monitoring and automated tracking of expiration dates are essential for maintaining valid certificates and adherence to compliance standards. Robust revocation processes, including CRLs and OCSP, are crucial to promptly invalidate compromised certificates and maintain system integrity. Automation streamlines management processes, ensures timely updates, and enhances compliance readiness through real-time monitoring and thorough documentation.
Understanding Control Certificates and Their Importance
Control certificates serve as essential components in the domain of cloud security, ensuring the integrity and authenticity of digital transactions.
These certificates act as digital endorsements, confirming the identity of users, devices, and services within cloud environments. By establishing a secure connection, control certificates help prevent unauthorized access and data breaches, thereby enhancing overall trust in cloud services.
They play a pivotal role in data encryption, ensuring that information remains confidential during transmission.
Additionally, compliance with regulatory standards often hinges on the proper management of these certificates.
As organizations increasingly rely on cloud infrastructure, understanding the importance of control certificates becomes vital for safeguarding sensitive information and maintaining robust security protocols in a rapidly evolving digital landscape.
The Control Certificate Lifecycle: An Overview
The control certificate lifecycle encompasses several critical stages that guarantee the effective management and security of digital identities within cloud environments.
The control certificate lifecycle is vital for managing and securing digital identities in cloud environments.
This lifecycle begins with the creation of control certificates, where key pairs are generated and certificates are issued, establishing trust.
Following issuance, the management phase involves maintaining and updating certificates to reflect changes in security policies and organizational needs. Monitoring is essential during this phase to detect any anomalies or potential breaches.
Eventually, certificates reach their expiration or revocation point, at which time proper procedures must be followed to guarantee secure decommissioning.
Throughout this lifecycle, adherence to compliance regulations and best practices is essential, as it helps organizations mitigate risks associated with identity management in cloud infrastructures.
Key Stages of Control Certificate Lifecycle Management
In the domain of control certificate lifecycle management, several key stages are critical to guarantee effective governance.
These include the certificate issuance process, management of renewal and expiration, and adherence to security compliance and auditing standards.
Understanding these stages is essential for maintaining the integrity and security of cloud-based systems.
Certificate Issuance Process
Issuing certificates in a cloud environment involves several key stages that assure secure and efficient management of digital identities.
Initially, the request for a certificate is generated, often triggered by an application or user needing authentication. This request is then submitted to a Certificate Authority (CA), where it undergoes verification to confirm the identity of the requester.
Upon successful validation, the CA issues the certificate, which includes essential information such as the public key and the issuer's details.
The newly issued certificate is then distributed to relevant entities, enabling secure communication and transactions.
Throughout this process, adherence to security protocols and standards guarantees the integrity and trustworthiness of the issued certificates, forming a vital part of the overall lifecycle management.
Renewal and Expiration Management
Renewal and expiration management play important roles in maintaining the security and validity of digital certificates within the cloud. As certificates approach their expiration dates, organizations must initiate renewal processes to prevent disruptions in service and guarantee continued trust.
This involves monitoring expiration timelines, evaluating certificate usage, and submitting renewal requests in a timely manner. Automated systems can streamline this process, reducing the risk of human error and confirming that certificates are updated without delay.
Additionally, organizations should establish policies for graceful alterations, including the revocation of expired certificates. Effective management of renewal and expiration not only safeguards data integrity and confidentiality but also reinforces compliance with industry standards and regulations.
Proper oversight in this stage is vital for maintaining a secure cloud environment.
Security Compliance and Auditing
Maintaining security compliance and conducting thorough audits are essential components of effective certificate lifecycle management. Organizations must adhere to regulatory requirements and industry standards, ensuring that all certificates are issued, managed, and revoked in alignment with security protocols.
Regular audits help identify any discrepancies or vulnerabilities within the certificate management process, allowing organizations to rectify issues promptly. Automated tools can facilitate compliance checks, enabling real-time monitoring of certificate statuses and expiration dates.
Additionally, extensive documentation of certificate usage and policies contributes to a transparent audit trail, which is vital during compliance assessments. By prioritizing security compliance and audits, organizations can mitigate risks associated with certificate mismanagement and uphold the integrity of their digital communications.
Best Practices for Issuing Control Certificates
In the management of control certificates, establishing clear certificate requirements is vital for ensuring compliance and effectiveness.
Streamlining approval processes can greatly enhance efficiency, reducing delays in issuance.

Additionally, monitoring expiration dates is imperative to maintain the validity and relevance of certificates over time.
Define Certificate Requirements

Establishing robust certificate requirements is vital for the effective management of control certificates in the cloud. Organizations must identify specific attributes and criteria for issuing certificates, including validity periods, encryption standards, and the intended use of each certificate.
This process should encompass compliance with industry regulations and internal security policies to guarantee alignment with organizational objectives. Additionally, it is important to define the roles and responsibilities of personnel involved in certificate issuance, including oversight mechanisms for monitoring adherence to these requirements.
Streamline Approval Processes
Although effective approval processes are essential for issuing control certificates, organizations often encounter bottlenecks that hinder timely certificate management.
To streamline these processes, organizations should implement standardized workflows that clearly define roles and responsibilities. Utilizing automated systems can facilitate prompt notifications and reminders, ensuring stakeholders remain engaged throughout the approval cycle.
Establishing clear criteria for approval helps reduce ambiguity and accelerates decision-making. Additionally, organizations can benefit from creating a centralized repository for documentation, allowing easy access to necessary information during the review process.
Regularly reviewing and refining approval workflows based on feedback can further enhance efficiency. By adopting these best practices, organizations can minimize delays in certificate issuance and improve overall management in the cloud environment.
Monitor Expiration Dates
Monitoring expiration dates is essential for maintaining compliance and guaranteeing the validity of control certificates. Organizations should implement automated tracking systems to alert stakeholders well in advance of impending expirations.
Regular audits can also help in identifying certificates nearing their expiration, thereby allowing ample time for renewal actions. Establishing a centralized repository for all control certificates can facilitate easy access and management of expiration data.
Additionally, assigning responsibility for monitoring these dates to specific personnel guarantees accountability and reduces the risk of oversight. By integrating these practices into their control certificate management strategy, organizations can effectively mitigate risks associated with expired certificates and uphold compliance standards in their cloud environments.
Renewal Strategies for Control Certificates
Effective renewal strategies for control certificates are essential for maintaining compliance and security within cloud environments. Organizations should implement automated tracking systems to monitor certificate expiration dates and initiate renewal processes in advance.
Establishing clear policies detailing responsibilities for certificate management can enhance accountability among team members. Additionally, utilizing centralized management tools can streamline the renewal workflow, reducing the risk of human error.
It is beneficial to conduct regular audits to evaluate the effectiveness of renewal strategies and guarantee adherence to industry standards. Training staff on the importance of timely renewals https://aquipress.com/top-rated-pki-management-platform-unveiled/ can foster a culture of vigilance regarding certificate management.
Revocation Processes and Their Significance
When control certificates are compromised or no longer needed, implementing a robust revocation process becomes essential for maintaining security in cloud environments. Revocation guarantees that unauthorized parties cannot exploit outdated or invalid certificates, thereby safeguarding sensitive data and maintaining trust.
The significance of this process lies in its ability to promptly invalidate certificates, preventing potential breaches. Effective revocation mechanisms, such as Certificate Revocation Lists (CRLs) and Online Certificate Status Protocol (OCSP), facilitate real-time verification of certificate validity.
Additionally, organizations must regularly audit and update their revocation policies to adapt to emerging threats. Ultimately, a well-defined revocation process is critical in minimizing security risks and guaranteeing the integrity of cloud-based systems, thereby reinforcing the overall security posture.
The Role of Automation in Lifecycle Management
The increasing complexity of control certificate management in cloud environments necessitates the incorporation of automation into lifecycle management processes. Automation streamlines the issuance, renewal, and revocation of certificates, greatly reducing the risk of human error.
By utilizing automated workflows, organizations can guarantee timely updates and compliance with regulatory requirements, thereby enhancing operational efficiency. Additionally, automation facilitates real-time monitoring of certificate statuses, allowing for proactive management of potential vulnerabilities.
This proactive approach minimizes downtime and strengthens overall security posture. As cloud environments evolve, the role of automation becomes increasingly crucial, enabling organizations to manage certificates seamlessly while focusing on core business objectives.
Ultimately, automation in lifecycle management not only enhances security but also optimizes resource allocation.
Leveraging Cloud Technologies for Enhanced Security
While traditional security measures often fall short in addressing the unique challenges of cloud environments, leveraging cloud technologies can greatly enhance overall security.
Cloud-native tools, such as automated threat detection and response systems, enable organizations to identify vulnerabilities in real-time. Additionally, the use of encryption technologies guarantees that data remains secure both at rest and in transit.
Multi-factor authentication and identity management solutions additionally strengthen access controls, reducing the risk of unauthorized access. Moreover, centralized logging and monitoring capabilities allow for thorough oversight of cloud environments, facilitating quick incident response.
Ensuring Regulatory Compliance Through Effective Management
Organizations must prioritize regulatory compliance to navigate the complexities of cloud environments effectively.
Effective management of control certificates is vital for aligning with various regulations and standards. This includes:
Regular Audits: Conducting systematic evaluations of cloud systems guarantees compliance with industry regulations, identifying potential gaps and areas for improvement. Documentation Management: Maintaining thorough records of all control certificates and their life cycles aids in demonstrating compliance during audits and assessments. Training and Awareness: Providing ongoing education for employees about regulatory requirements and compliance protocols fosters a culture of accountability and vigilance.FAQ
How Can I Track Control Certificate Expiration Dates Effectively?
Tracking control certificate expiration dates effectively involves establishing a systematic approach.
One method is to create a centralized database where all certificates and their expiration dates are recorded. Regular audits and reminders can be scheduled to guarantee timely renewals.
Utilizing automated tools can enhance tracking efficiency, allowing for real-time updates and alerts as expiration dates approach.
This proactive strategy minimizes the risk of lapses in certification and maintains compliance with necessary standards.
What Are the Costs Associated With Control Certificate Management in the Cloud?
The costs associated with managing control certificates typically include subscription fees for cloud services, expenses for automation tools, and labor costs for personnel overseeing the management process.
Additionally, organizations may incur costs related to training staff on compliance protocols and potential penalties for non-compliance.
Maintaining security measures and ensuring timely renewals can also add to the overall financial commitment.
Budgeting for these factors is essential for effective certificate management.
Can Control Certificates Be Transferred Between Different Cloud Providers?
The transfer of control certificates between different cloud providers is generally feasible, but it depends on the specific certificates and the providers' policies.
Typically, certificates issued by a recognized Certificate Authority can be exported and imported.
However, compatibility issues may arise due to differing security protocols or certificate formats.
Organizations must also consider the implications for compliance and security when moving certificates, ensuring that the transfer aligns with their governance frameworks.
What Tools Are Available for Automating Control Certificate Management?
Automating control certificate management involves various tools designed to streamline the process.
Options include certificate management platforms like Venafi, DigiCert, and Let's Encrypt, which offer features for issuance, renewal, and revocation.
Additionally, configuration management tools such as Ansible and Terraform can help automate certificate deployment across systems.
These tools enhance security and efficiency by reducing manual interventions, ensuring that certificates are up-to-date and compliant with organizational policies and regulatory requirements.
How Do I Handle Control Certificates for Hybrid Cloud Environments?
In a hypothetical scenario, a financial institution operates both on-premises and in the cloud, requiring seamless control certificate management.
To handle control certificates in hybrid cloud environments, organizations should implement a centralized management system that automates certificate issuance and renewal. Integration with existing infrastructure guarantees compliance and minimizes downtime.
Regular audits and monitoring tools are essential to maintain security and mitigate risks associated with certificate expiration and misconfiguration in such complex setups.
Conclusion
In the domain of cloud security, control certificates act as sentinels guarding the fortress of data. Their lifecycle, akin to the seasons, demands careful tending. Just as spring brings renewal and autumn signals reflection, organizations must embrace best practices and automation to nurture these certificates. By doing so, they not only fortify their defenses but also guarantee compliance with the laws of the digital kingdom, ultimately safeguarding the treasures of information that lie within.